Enterprise architecture for banking transformation
Target-state architecture, integration choices and review logic for core platforms, payments, data and regulated change programmes.


PiR2-IT helps regulated organisations design secure platforms, recover difficult programmes and move from strategy to controlled delivery with clearer governance, stronger architecture and implementation-aware execution.
Looking for delivery examples? See selected projects.
PiR2-IT is an execution-oriented consulting and engineering practice focused on complex digital systems operating in regulated, mission-critical and high-trust environments. Our work connects enterprise architecture, cybersecurity, AI enablement, governance and advanced prototyping so that strategy can be translated into systems that are secure, scalable, auditable and operationally real.
We operate at the intersection of architecture strategy and real implementation. That means platform design is evaluated not only for structure and compliance, but also for delivery feasibility, operational resilience, cost discipline and evidence-led governance.
PiR2-IT supports organizations that must balance security, scalability, regulatory expectations and operational reliability across banking, defence, AI, digital trust and other high-consequence environments.

Architecture assessments, target-state design, integration strategy and executable roadmaps for secure, scalable platforms.

Security-by-design, Zero Trust patterns, cyber architecture reviews and defensible control structures for high-stakes environments.

AI governance, data architecture, MLOps and production-readiness for organisations moving from pilots to controlled AI adoption.

Governance frameworks, decision rights, KPI control and executive oversight for complex programmes that need clearer execution.

Controlled prototypes, technical validation and proof-of-feasibility work for emerging digital and cyber-physical systems.
Reference architectures, integration patterns, scalable platform design and second-opinion reviews for complex enterprise and regulated systems.
Cyberspace definition, AI-enabled detection, intrusion monitoring, resilience controls and defensible security architecture.
Data governance, AI operating models, MLOps structures and production-ready AI enablement for enterprise and mission-critical environments.
Independent architecture review and redesign of a large-scale banking environment.
Specialized AI-supported detection model integrated into operational cyber defence workflows.
Production-grade AI pipeline redesign with governance, MLOps and monitoring controls.
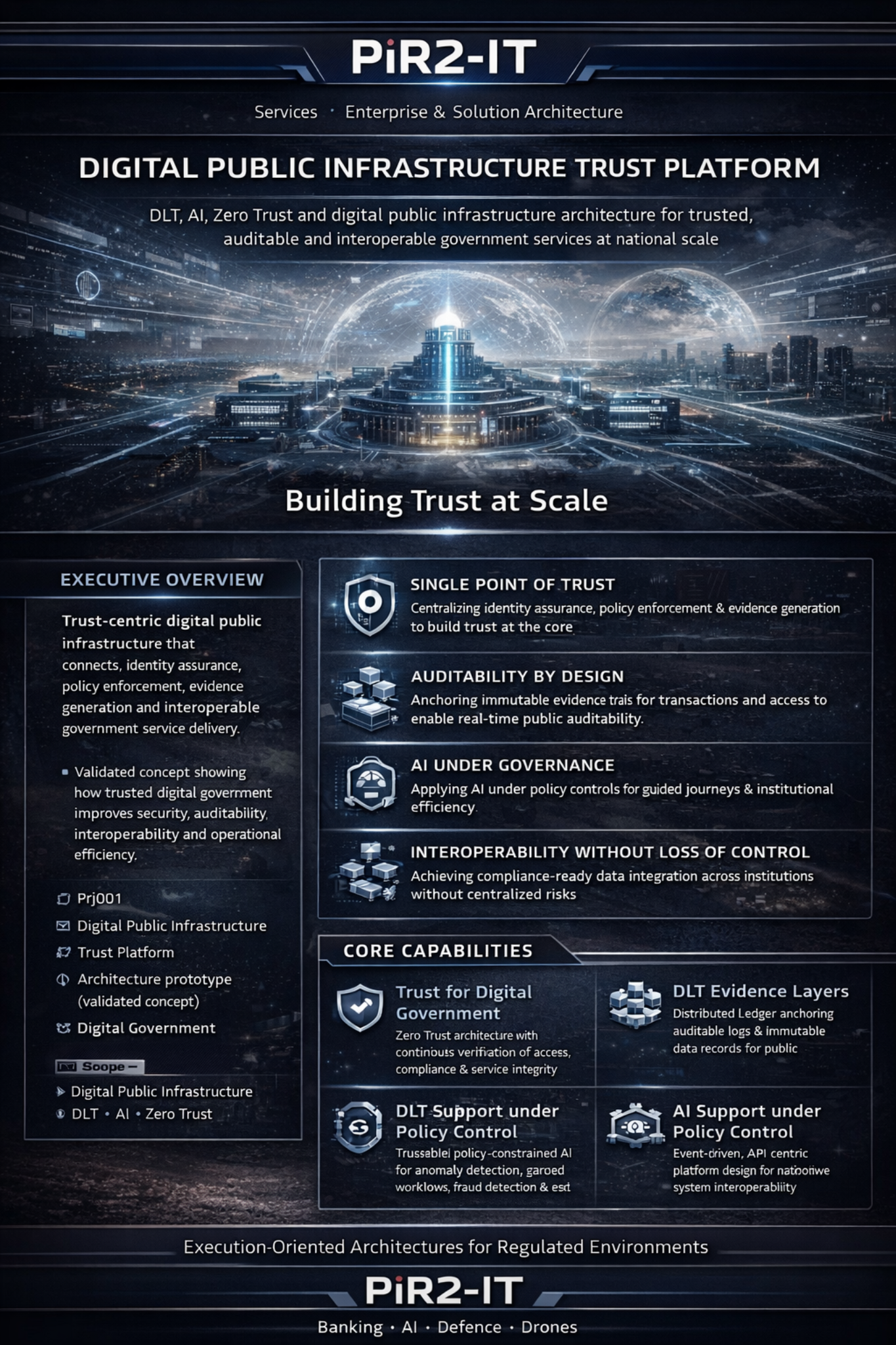
Digital public infrastructure architecture combining DLT, AI and Zero Trust for trusted national-scale services.
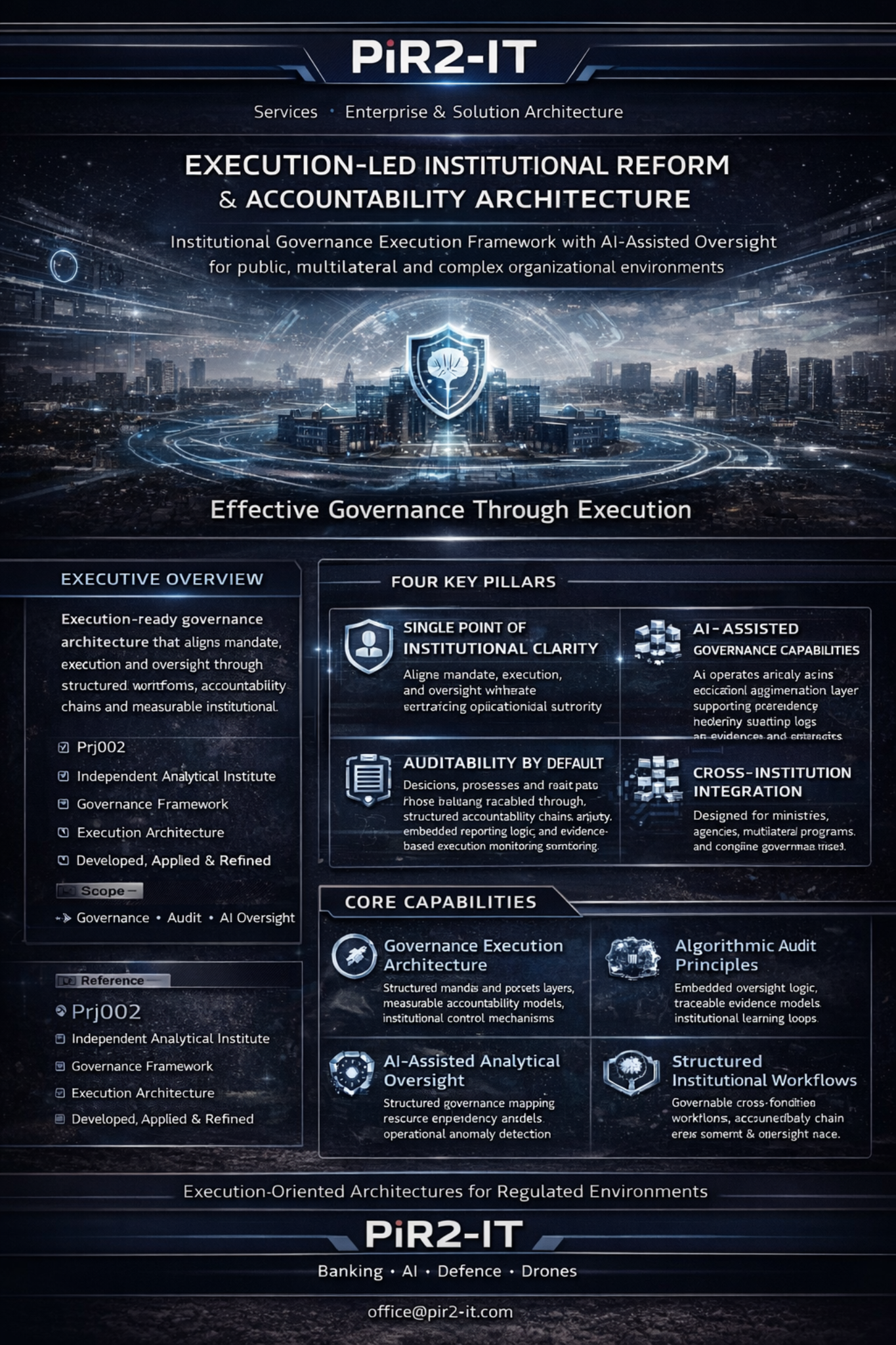
Execution-led institutional reform architecture for accountability and oversight.
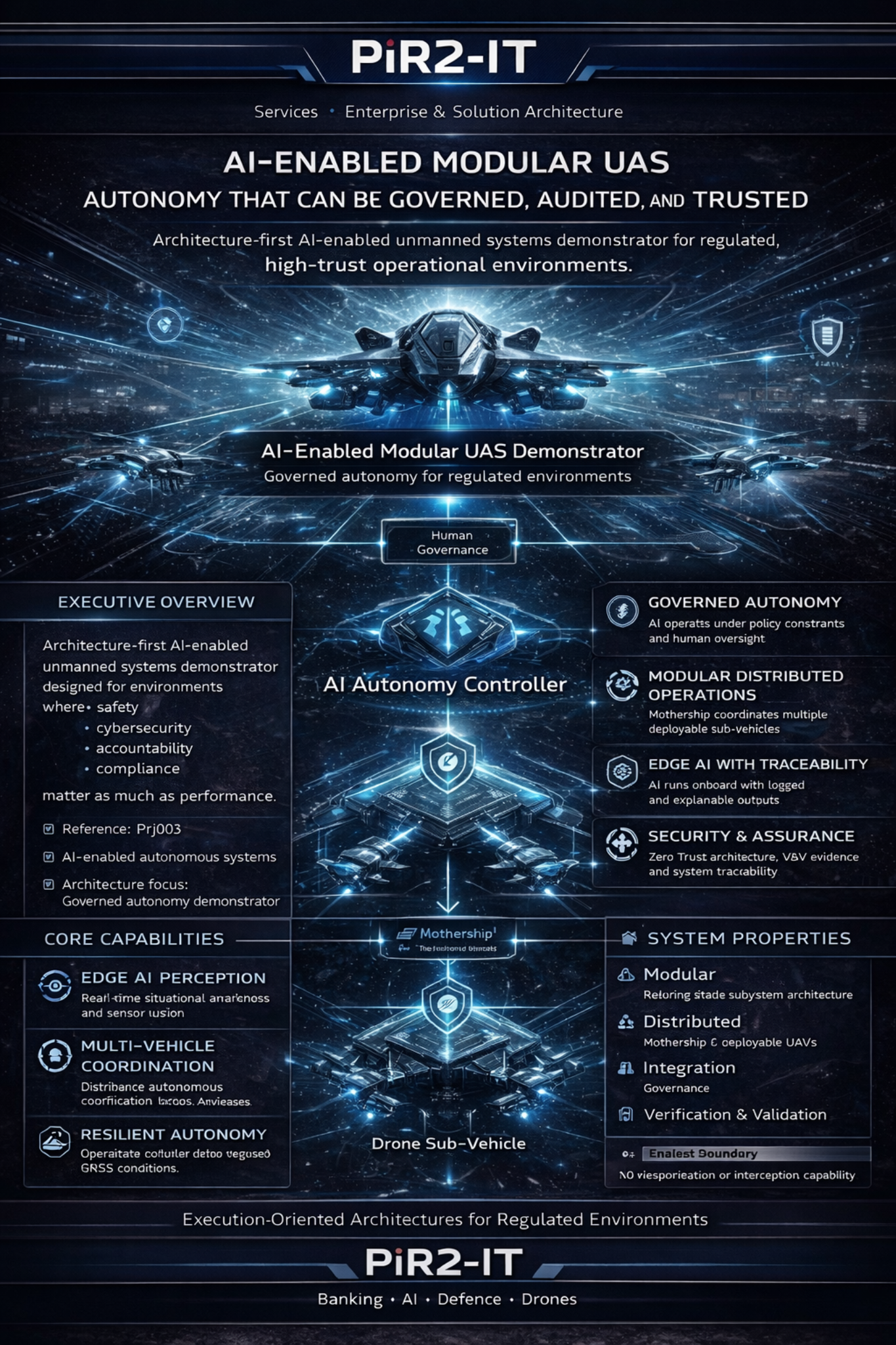
AI-enabled modular unmanned systems demonstrator with assurance, cybersecurity and auditability by design.

Radar and camera sensor fusion platform for governed autonomous mobility and audit-ready AI engineering.
Target-state architecture, integration choices and review logic for core platforms, payments, data and regulated change programmes.
Security architecture, trust boundaries and control design for defence, mission-critical and high-consequence digital environments.
AI operating models, control structures, data foundations and accountable deployment patterns for organisations that cannot improvise governance.
Architecture and delivery guidance for identity, trust, interoperability and service-design led government modernisation.
PMO logic, KPI structures and decision traceability for transformations that involve multiple vendors, institutions or executive sponsors.
Usually when a programme is large enough that architecture quality, governance quality and delivery sequencing materially affect cost, risk or sponsor confidence.
No. The positioning is advisory-led, but the work is delivery-aware: architecture reviews, governance packs, control design, integration logic, prototypes and programme decision support.
Banking, public sector and digital public infrastructure, defence and mission-critical systems, plus other regulated environments where security, resilience and traceability matter.
Yes. Enterprise architecture often connects with cybersecurity architecture, AI governance or delivery governance when a transformation needs stronger design control end to end.